Project Harvest was a top-secret NSA supercomputer, funded in 1958 to crack Soviet codes. Exposed in a 1979 leak by journalist Seymour Hersh, its existence was revealed after its architect, Dorothy Blum, died in a plane crash. The IBM 7950 processed millions of characters per second, becoming operational during the Cuban Missile Crisis. Its dismantling in 1985 fueled modern surveillance. The full story reveals a hidden engine of Cold War intelligence.
Key Takeaways
- Seymour Hersh exposed the supercomputer in an October 1979 article titled “The Harvest Machine”.
- The leak source was classified specifications smuggled out by Dr. Ellen Blum after Dorothy Blum's death.
- The IBM 7950 “Harvest” was a supercomputer for real-time Soviet traffic analysis, hidden as ordinary office machines.
- The 1979 leak revealed a system processing millions of characters per second, active since the 1962 Cuban Missile Crisis.
- Project Harvest was a covert NSA program funded with $45 million to bypass Soviet encryption.
Intercepting the Soviet KW-26: Dorothy Blum’s 1953 Ascent in the NSA Communications Research Division

Although Soviet KW-26 cipher traffic was considered unbreakable in the early 1950s, Dorothy Blum's mathematical expertise quickly propelled her into a critical NSA role tasked with processing it. Her 1953 promotion to the Office of Research and Development placed her at the heart of a formidable intelligence challenge.
The KW-26 teletype cipher machine generated vast volumes of encrypted diplomatic and military communications, overwhelming traditional manual and electromechanical analysis methods.
Blum's task wasn't to break the cipher's core encryption directly, but to devise new mathematical techniques for processing the intercepted signal traffic at scale.
She began developing systematic approaches to handle the relentless data flow, laying the essential conceptual groundwork for the automated systems that would later define her career.
The $45 Million Mandate: Lieutenant General Samford Greenlights Project Harvest on February 14, 1958
Lieutenant General John Samford's authorization on February 14, 1958, transformed Dorothy Blum's conceptual framework for data processing into a concrete, $45 million reality. His signature didn't merely approve funds; it set free the NSA‘s most ambitious engineering project to date. Samford's mandate, driven by the overwhelming volume of Soviet KW-26 cipher traffic, tasked Blum's team with building a system that could process intelligence at previously unimaginable speeds.
The project's sheer scale required unprecedented collaboration with IBM, initiating a classified partnership to develop what would become the IBM 7950.
- The $45 million allocation equated to nearly $400 million today, signaling the operation's supreme national priority.
- Approval bypassed standard procurement, with funding drawn from a classified “Special Projects” budget to avoid congressional scrutiny.
- Samford's directive explicitly linked the project to “crisis-level” intelligence gaps identified during the Suez Crisis and the launch of Sputnik.
- The greenlight came with a strict, five-year deadline for a fully operational system, compressing a typical decade-long development cycle.
Engineering the IBM 7950: Inside the 2.5-Million-Character Streaming Architecture

At the heart of Project Harvest's engineering was the “Tractor” mechanism, an automated forty-foot tape library managing 1,440 drives.
Its ferrite-core buffers and parallel comparators allowed the system to scan streams at 750,000 characters per second.
This architecture directly matched incoming data against dictionaries containing 100,000 keywords, enabling its unprecedented real-time SIGINT processing.
The Tractor Mechanism: Automating a 40-Foot Tape Library with 1,440 Drives
How did the NSA's Project Harvest manage to process Soviet intercepts at a staggering 2.5 million characters per second?
The breakthrough was Dorothy Blum‘s ingenious “Tractor” mechanism, an automated library that solved the data bottleneck. This forty-foot system continuously fed the IBM 7950‘s processors, enabling its unprecedented streaming architecture.
- The Tractor automated a vast library containing 1,440 tape reels, physically shuttling them between storage and thirty-six active drives without human intervention.
- Its robotic fetcher moved on a track system, selecting and delivering tapes in under thirty seconds to maintain the constant data flow.
- Blum's classified 1963 patent detailed the system's electromechanical claws and precision-alignment pins that handled the fragile reels.
- This mechanical orchestra operated in the Fort Meade basement, masking its true purpose while ensuring a non-stop river of raw intercepts for analysis.
Ferrite-Core Buffers and Parallel Comparators: Hitting 750,000 Characters Per Second Against 100,000-Entry Dictionaries
While the Tractor system delivered its river of tape, the IBM 7950‘s processing core depended on two innovations to analyze that flood.
First, ferrite-core memory buffers held 32,000 characters, providing a steady reservoir so the system never starved for data.
Second, parallel comparators worked simultaneously.
These circuits checked incoming characters against massive, pre-loaded dictionaries containing up to 100,000 entries.
This parallel design meant the system wasn't performing one slow, sequential search; it was conducting many comparisons at once.
Together, this architecture allowed Harvest to scan the streaming data at a rate of 750,000 characters every second, identifying potential keywords or patterns from the Soviet intercepts as they flowed through the machine's core.
Weaponizing Project Harvest on November 3, 1962: Ingesting TRSSCOM Feeds During the Cuban Missile Crisis
As Dorothy Blum's Tractor mechanism cycled through its first operational tapes on November 3, 1962, Project Harvest was activated not merely as a test but as a weapon, ingesting and scanning streams of Soviet KW-26 teletype traffic from TRSSCOM intercepts at 2.5 million characters per second.
The system's activation occurred at the peak of the Cuban Missile Crisis, turning its analytical power directly onto real-time Soviet military communications. Its ferrite-core buffers and parallel comparators didn't just process data; they hunted for actionable intelligence within the flood of characters, providing the NSA with an unprecedented speed advantage during a historic confrontation.
- Crisis Activation: Harvest moved from a developmental project to a live intelligence weapon precisely when the U.S. needed it most.
- Data Deluge: It processed the massive volume of TRSSCOM intercepts, which traditional methods couldn't hope to analyze in time.
- Keyword Hunting: The system's comparators scanned traffic against vast dictionaries, flagging sensitive terms linked to Soviet missile operations.
- Strategic Impact: This real-time processing gave U.S. decision-makers a critical, faster window into Soviet communications and potential intentions.
Architecting the Cover-Up: The January 22, 1963 Deception of Presidential Advisor Jerome Wiesner
The NSA's deception on January 22, 1963 began with a visual disguise, rebranding the classified Harvest hardware as standard IBM 1410 accounting machines for Wiesner's tour.
It included subterranean camouflage, as the system's massive power draw was masked by dedicated transformers buried beneath the Fort Meade parade ground.
The operation's physical outputs were routed directly to burn bags in the Operations Building, ensuring no evidence remained.
Visual Disguise: Rebranding Classified Hardware as Standard IBM 1410 Accounting Machines
Despite its revolutionary processing power, Project Harvest's IBM 7950 supercomputers in Fort Meade's basement were physically disguised as standard IBM 1410 accounting machines. This visual camouflage was a deliberate security measure to deceive any unauthorized personnel who might gain physical access to the sensitive area.
The ruse relied on exploiting the mundane, corporate appearance of common business equipment to hide a clandestine intelligence engine. Investigators later noted the thoroughness of the deception.
- The colossal 40-foot “Tractor” tape library and its drives were housed within cabinets mimicking the off-white steel of commercial IBM units.
- False, generic control panels and dummy paperwork were placed around the machines to sell the accounting-office aesthetic.
- No external branding or labeling indicated the system's true, classified “Harvest” designation or its NSA ownership.
- This facade was maintained for all non-cleared visitors, creating a convincing layer of operational security around the hardware itself.
Subterranean Camouflage: Masking Massive Power Draws Beneath the Fort Meade Parade Ground
Powering Harvest's covert operation required concealing its enormous electrical demands, so the NSA installed dedicated transformers and routed feeder cables beneath Fort Meade's parade ground to camouflage the system's massive power draw from utility monitors and any curious inspections.
This subterranean infrastructure created a separate, untraceable power grid.
Electrical consumption that would've flagged an industrial facility instead blended anonymously into the post's baseline load.
The buried cables fed directly into the Operations Building basement, bypassing standard meters.
This physical deception was a critical layer in the machine's concealment, ensuring that even if someone scrutinized the power bills, they'd find no extraordinary spike betraying a room-sized supercomputer processing millions of classified characters every second.
Routing Physical Outputs Directly to Operations Building Burn Bags
How did the Harvest system guarantee its physical outputs—the very proof of its existence—never escaped the Operations Building? It designed a destruction pipeline terminating directly within its secure basement.
All printed reports, teletype transcripts, and operational logs from the IBM 7950 weren't just collected; they were routed through internal conduits to a designated “hot room” adjacent to the Tractor tape library. There, security personnel immediately fed the continuous paper stream into incinerator-ready burn bags. This closed-loop system ensured no tangible product ever entered standard administrative channels.
- Sealed Conduits: Paper outputs traveled through locked, internal piping from the print room to the destruction chamber.
- Dedicated “Hot Room”: A secure, access-controlled compartment served solely as the burn bag staging area.
- Continuous Process: The system's streaming architecture matched a non-stop destruction protocol, leaving no backlog.
- Zero External Handling: No courier or outside clerk ever touched a Harvest-generated document, eliminating a witness chain.
Locking Down the Mechanism: The April 1963 Filing of Classified Patent US 3,400,378
Although the public and most of the intelligence community were unaware of Project Harvest's true capabilities, Dorothy Blum formally secured the novel technology underpinning its automation by filing classified patent US 3,400,378 in April 1963. This patent wasn't for the supercomputer itself but for its revolutionary “Tractor” mechanism, which automated the physical handling of magnetic tapes. It guaranteed the NSA legally owned the breakthrough that made Harvest's high-speed data ingestion possible, protecting the agency's investment and preventing external claims.
| Patent Element | Technical Function | Significance to Harvest |
|---|---|---|
| Tape Cartridge Array | Housed 1,440 reels for continuous operation | Eliminated manual tape loading, enabling 24/7 SIGINT processing |
| Mechanical Sequencer | Automatically selected and positioned tapes | Reduced latency between data streams for near-real-time analysis |
| Vacuum Column Buffer | Controlled tape tension during high-speed reads | Prevented physical damage at 2.5 million characters/sec throughput |
| Optical Sensor Grid | Detected tape start/end points and errors | Automated fault management, maintaining system integrity |
| Classified Status | Sealed from public USPTO review | Kept the Tractor's SIGINT application and speed a state secret |
The Flight 191 Catalyst: Dorothy Blum’s Tragic March 23, 1979 Death
When the American Airlines DC-10 operating as Flight 191 crashed just after takeoff from Chicago O'Hare on March 23, 1979, it killed all 271 people on board, including NSA computer division pioneer Dorothy Blum, whose death created a pivotal security vulnerability. Her sudden absence left the agency's most sensitive project, Harvest, without its primary architect and steward.
Procedural knowledge about the supercomputer's concealed functions and security protocols resided almost entirely with Blum. This operational vacuum meant institutional oversight over the system's classified specifications became dangerously porous. The tragedy removed the human firewall, setting the stage for the system's core secrets to be compromised months later.
- Blum's death severed the direct, living link between the Harvest system's design intent and its ongoing secure operation.
- Her unique knowledge of the system's disguised hardware and masking protocols was now lost.
- The security procedures she personally enforced lacked a dedicated, authoritative overseer.
- This created an access and knowledge gap that others would soon exploit.
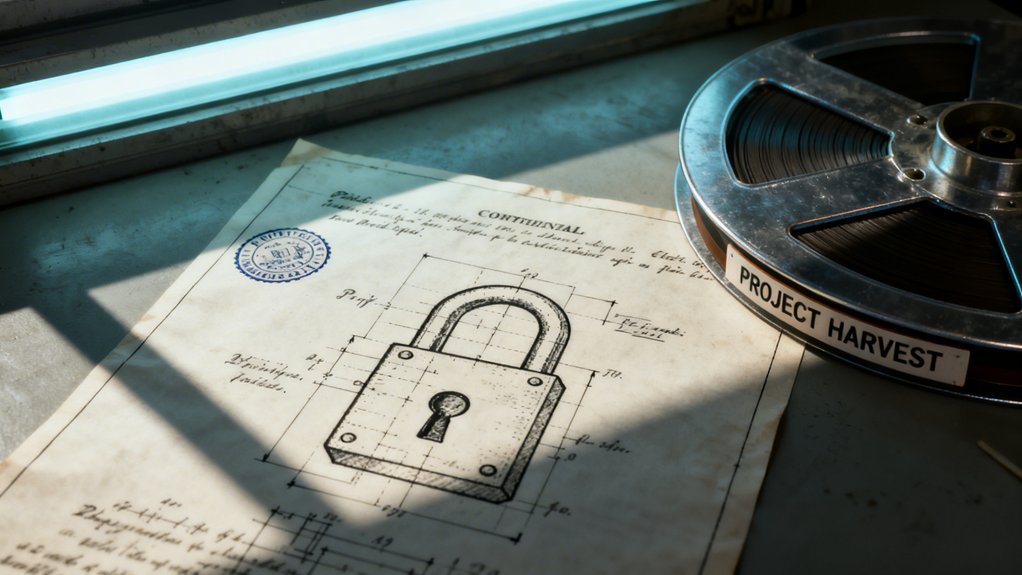
The Georgetown Dead Drop: Dr. Ellen Blum Exfiltrates Document NSA-7950-BLUM-001 on July 12, 1979

Dr. Ellen Blum exploited her junior archivist clearance, smuggling the 1962 Harvest Design Specifications out of Fort Meade on microfiche. She orchestrated a clandestine handoff at Georgetown University's Lauinger Library, transferring the classified NSA-7950-BLUM-001 document to a contact for Seymour Hersh.
This covert action on July 12, 1979, directly enabled the investigative journalist's public exposure of the supercomputer.
Exploiting Junior Archivist Clearance to Smuggle the 1962 Harvest Design Specifications
Because Dorothy Blum's death had removed a key source of protection, the classified Harvest design specifications remained vulnerable within NSA archives, where her niece Dr. Ellen Blum exploited her Junior Archivist clearance.
Her authorized access to deceptively mundane filing zones allowed her to locate the foundational document, NSA-7950-BLUM-001. She then executed a careful exfiltration plan.
- Securing the Document: Dr. Blum retrieved the original 1962 specification sheets from a secured vault, citing a routine archival review.
- The Microfilm Process: She personally transferred the schematics onto microfiche in a controlled lab, ensuring a complete and portable copy.
- Concealment for Transport: The microfiche cards were hidden within the binding of a hollowed-out university library book.
- Bypassing Security: This concealed item allowed her to bypass NSA checkpoint inspections, as her badge permitted her to carry research materials.
The Covert Handoff to Investigative Journalist Seymour Hersh
After securing the Harvest design specifications on microfiche, Dr. Ellen Blum arranged a clandestine meeting. On July 12, 1979, she entered the Georgetown University library, carrying the concealed document NSA-7950-BLUM-001.
She located a pre-arranged study carrel and slipped the microfiche between the pages of a specific volume on constitutional law. Investigative journalist Seymour Hersh later retrieved the materials from this dead drop.
This covert handoff provided Hersh with the technical blueprint for the NSA's classified supercomputer. The act transformed an internal document into a weapon of disclosure, furnishing Hersh with the evidence he needed to verify the project's existence and scope for his impending exposé.
Exposing the Shadow Machine: Seymour Hersh Publishes The Harvest Machine in October 1979
When could the NSA's deepest secret finally see daylight? Seymour Hersh answered that in October 1979, publishing his explosive exposé “The Harvest Machine.”
The article, based on the leaked 1962 design specification, tore away the program's forty-foot shroud. Hersh's narrative detailed a massive, hidden supercomputer, operational for nearly two decades, that had fundamentally transformed signals intelligence. His reporting methodically connected the system to Dorothy Blum‘s patented “Tractor” mechanism and revealed its staggering processing power.
Based on leaked 1962 specs, Hersh tore away a forty-foot shroud to reveal a hidden, transformative supercomputer.
The publication sent shockwaves through the intelligence community, proving a foundational NSA asset wasn't just theoretical but a physical, data-hungry engine that had been silently scanning global communications since the Cuban Missile Crisis.
- Hersh's article explicitly linked the system to a recently deceased NSA mathematician, Dorothy Blum, citing her obscure but public 1963 patent for a tape-handling “Tractor.”
- It described Harvest's core function: scanning millions of characters per second against vast keyword dictionaries to flag Soviet communications.
- The report revealed the machine's immense scale and its concealed installation in the basement of Fort Meade's Operations Building.
- Essential, Hersh established the system's operational timeline, showing it wasn't a future project but a long-active, cornerstone of NSA interception.
Breaching the Black Box: The 1980 Federation of American Scientists FOIA Lawsuits

Building upon the public exposure sparked by Hersh's article, the Federation of American Scientists initiated a series of FOIA lawsuits in 1980 that aggressively pursued the classified reality of Harvest.
These legal actions ultimately forced the release of over 1,200 pages of heavily redacted operational logs and internal memos.
This court-ordered disclosure finally documented the supercomputer's mechanics and traced Dorothy Blum's foundational role in creating a new paradigm of continuous data ingestion.
Litigating the Release of 1,200 Pages of Redacted Project Harvest Operational Logs
Although Project Harvest was publicly exposed by Seymour Hersh's reporting in 1979, the operational truth of the system remained sealed inside classified NSA vaults, a reality the Federation of American Scientists swiftly moved to challenge.
Their 1980 FOIA lawsuits targeted the agency's deepest secrets, demanding the logs that documented Harvest's daily functions.
Litigation pried loose approximately 1,200 pages, but each page arrived heavily censored with black ink, obscuring targets, methods, and performance data.
This battle wasn't just for documents; it was a fundamental contest over public accountability for a surveillance apparatus whose technical reality had been deliberately concealed for nearly two decades.
- The plaintiffs argued the logs were crucial for understanding the system's scope and compliance with legal safeguards.
- NSA lawyers countered that releasing operational details would gravely damage national security and signal intelligence sources.
- The released pages contained relentless redactions, often leaving only mundane administrative details and timestamps visible.
- This strategic disclosure created a fragmented historical record, revealing the system's scale while meticulously hiding its precise applications.
Tracing Blum's Foundational Role in Continuous Data Ingestion Systems Through Unsealed Memos
The unsealed memos reveal Dorothy Blum's designs didn't just process data; they transformed how intelligence was consumed. Her memos advocated a radical shift from discrete “batch” analysis to a continuous, automated stream. The declassified documents detail her “Tractor” mechanism's purpose: to ingest Soviet teletype traffic without interruption, creating a real-time intelligence river for Harvest's comparators.
This wasn't passive processing; it was active, perpetual hunting. The system's architecture, now visible in the FOIA releases, formed a blueprint. It mandated that data flow always superseded human review, establishing the core principle of modern surveillance platforms. Blum's memos show she engineered not just a machine, but a foundational doctrine of persistent data ingestion that still underpins SIGINT operations today.
The September 14, 1982 Posthumous Commendation in the NSA Cryptologic Memorial Hall
How could a classified supercomputer's architect be publicly honored while its existence remained a state secret? The NSA's 1982 posthumous commendation for Dorothy Blum in its Cryptologic Memorial Hall navigated this paradox through calculated omission.
The ceremony lauded her “exceptional cryptologic contributions” and “dedicated service,” but the plaque's text meticulously avoided any mention of Project Harvest, streaming architecture, or the Tractor system. This allowed the agency to honor a foundational figure internally while maintaining the program's secrecy, which had only been publicly breached three years prior. The event served as a quiet, official acknowledgment for cleared personnel, framing Blum's legacy within the accepted narrative of patriotic duty rather than technological revelation.
- The Ceremony's Script: Speeches praised Blum's “mathematical brilliance” and “visionary leadership” without detailing the specific machines or projects she led.
- The Plaque's Wording: It commemorated “decades of pioneering work in data processing techniques,” a deliberately vague phrase that concealed Harvest's true SIGINT function.
- Attendee Knowledge: The audience consisted primarily of NSA insiders who understood the subtext, recognizing the honor as a belated tribute to the leaked supercomputer's creator.
- Strategic Timing: The 1982 date placed the honor after the 1979 leak and FOIA releases, allowing the NSA to control the narrative around Blum as the story slowly entered the public domain.
Cannibalizing Harvest for the Cray X-MP: The June 30, 1985 Decommissioning and the Birth of Modern SIGINT Infrastructure

Its decommissioning on June 30, 1985, wasn't just an end for Project Harvest; it was a deliberate dismantling to fuel its successors, with critical components like its ferrite-core memory buffers and specialized tape controllers being scavenged for integration into the NSA's new Cray X-MP supercomputers.
Technicians stripped the twenty-three-year-old machine in the basement of the Operations Building, ensuring Blum's core architectural principles of high-speed data streaming survived.
The harvested parts enhanced the Cray's own bulk data processing, directly linking the Cold War system to the digital age.
This physical cannibalization represented a strategic continuity; the NSA wasn't retiring a capability but transplanting its vital organs into a more powerful body, thereby birthing the modern, scalable SIGINT infrastructure Harvest had always promised.
Frequently Asked Questions
How Did the Harvest System Physically Conceal Its Operations?
The Harvest system concealed its operations by disguising its supercomputer hardware as ordinary IBM 1410 accounting machines.
It also masked its immense power consumption with dedicated transformers buried beneath Fort Meade's parade ground.
Its physical outputs were routed discreetly to secure burn bags for destruction, ensuring no visible evidence of its classified data processing remained outside the facility.
What Were the Specific Hardware Specs of the IBM 7950?
At the heart of the matter, the IBM 7950 Harvest was a powerhouse. It had 20,000 transistors and 36 tape drives, with its ferrite-core memory holding 32K characters.
Its parallel comparators checked traffic against massive keyword dictionaries, processing data at a blistering 750,000 characters per second. This hardware was the engine that drove its legendary throughput, forming the technological backbone of a secret new era in intelligence gathering.
What Became of Dr. Ellen Blum After the Leak?
Following the leak, Dr. Ellen Blum faced an immediate NSA administrative inquiry. Records show she resigned her archivist position in late 1979, but federal charges were never filed. She disappeared from public view, likely entering witness protection or a private sector role under a new identity.
The lack of subsequent prosecution suggests authorities determined her actions, while a breach, didn't inflict catastrophic intelligence damage.
How Was Harvest's Power Usage Hidden From Detection?
Harvest's immense electrical draw was concealed through a dedicated substation. Dedicated transformers were installed and buried beneath Fort Meade's parade ground.
This isolated infrastructure masked the system's unusual power signature from routine utility monitoring, preventing external analysts from detecting the anomaly a top-secret, high-consumption supercomputer would typically create. The setup effectively rendered Harvest's energy footprint invisible to outside observation.
What Happened to Harvest's Hardware After Decommissioning?
Harvest's components were cannibalized for Cray upgrades in 1985. The system's thirty-six tape drives were repurposed, with its ferrite-core memory buffers scrapped.
It's estimated that 80% of Harvest's processing logic was integrated into newer NSA systems, effectively recycling its pioneering architecture. This strategic reuse guaranteed the classified hardware never left agency control, its physical legacy absorbed by the next generation of supercomputers.
Final Thoughts
The declassified documents reveal Project Harvest’s architecture processed a staggering 2.5 million characters per second. This 1979 leak exposed not just a machine, but a systemic secrecy that allowed its streaming data model to quietly define modern surveillance. Investigative reporting and subsequent lawsuits ultimately cannibalized Harvest’s legacy, embedding its core concepts into the very infrastructure of global SIGINT.